The anonymity of sellers and crypto payments reduces friction and complicates enforcement . The dark web ecosystem supplies not only goods but also how‑to guides and peer support, lowering the barrier to entry for novice fraudsters .
Introducing Data Fabric
The objective of carding is to identify which card numbers or details can be used to perform purchases. Learn how to automate financial risk reports using AI and news data with this guide for product managers, featuring tools from Webz.io and OpenAI. With the large number of illicit channels that exist on Telegram, we also see malware being distributed, ransomware being sold (as well as other hacking tools), step by step guides for cybercrime, and payment facilitation using cryptocurrencies for illicit transactions.
For a cyber thief, the beauty of stealing money from gift cards is that it is typically anonymous and untraceable once stolen. Every chargeback hurts a business’s reputation with credit card processors. Chargebacks can happen for legitimate reasons (for example an erroneous purchase or a clerical error), but are very often the result of fraud techniques like carding.
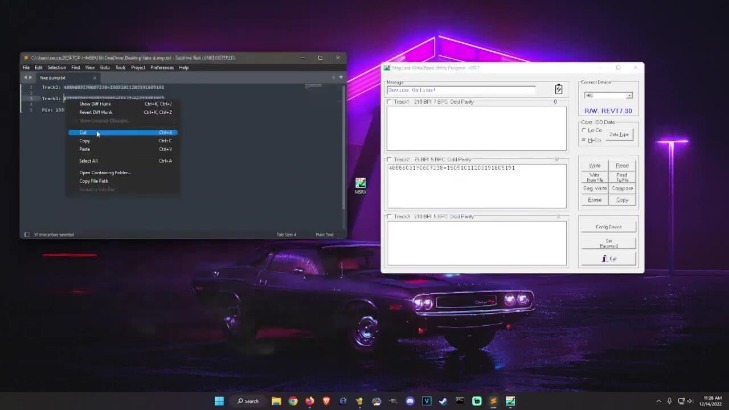
The following screenshot from DarkOwl’s Vision UI provides an example of sensitive data exposed in B1ack’s Stash’s recent free credit card dump. It was known for selling high-quality stolen payment card details and used blockchain-based domains to evade law enforcement. The market sells credit card information to users occasionally shares free credit card dumps (as seen below). Emerging on April 30, 2024, it quickly gained notoriety by releasing 1 million stolen payment card details for free, a strategy aimed at attracting cybercriminals to its platform. Many forums offer escrow services to facilitate safe transactions. Chatter on stolen data forums makes this sentiment all too clear; consumers are quick to label new vendors a ‘scam’ and suspect foul play as soon as their deposit arrives mere moments too late.
Teens Plead Not Guilty Over TfL Cyber-attack
Automatic payments get declined, travel plans get disrupted, and sorting everything out with the bank can take hours. Their payment processor raised their rates, and suddenly their already-thin margins became unsustainable. I’ve worked with family-owned businesses that nearly went under after getting hit with a wave of fraudulent purchases. Obviously, financial institutions bear the heaviest burden. These markets have evolved their own reputation systems, with escrow services and vendor ratings that mirror legitimate e-commerce platforms.
How Businesses Can Protect Themselves Against Carding
- The card number on a credit card is typically found in the top-left corner or along the front edge.
- The process of carding begins with card thieves, known as “carders,” who steal credit card information through phishing, skimming, conducting data breaches, or keylogging.
- Read this Dark Web Pulse to see examples of illicit content on Telegram and a thorough breakdown of why threat groups prefer instant messaging.
- Imagine waking up to discover thousands of fraudulent transactions on your site.
- Sellers often provide buyers with validity rates for their data and even offer replacements for cards that don’t work.
Talk to one of our cyber experts to learn how Lunar equips your team to uncover hidden threats and gain visibility into conversations that matter most. Uncover the threats that are relevant to you by leveraging Lunar’s continuous monitoring of the deep and dark web. With so many threat and APT groups actively using Telegram, the platform becomes a vital source of information. The group also promotes DDoS services and seeks visibility for its operations through proof-of-attack screenshots. The group claims to provide thousands of new logs daily, making it a consistent source of fresh compromised data.
How Do Carding Attacks Damage Businesses?
As B1ack’s Stash prepares to release its trove of stolen credit cards, law enforcement agencies and cybersecurity firms are working around the clock to trace the origins of these breaches and prevent further exploitation. The cybersecurity community is on high alert as B1ack’s Stash, a known marketplace on the dark web, has announced a massive leak of 4 million stolen credit card details. Carding is an automated form of payment fraud in which fraudsters test a bulk list of credit or debit card data against a merchant’s payment processing system to verify breached or stolen card details. After buying stolen credit card information, fraudulent actors use carding bots to validate the information.

Unlike many imitators, this is the official Hidden Wiki that maintains a curated directory of legitimate .onion services. It provides safety and anonymity for journalists, privacy-conscious users, or those in high-censorship countries. Using a reliable VPN with Tor provides a way to improve security when accessing dark web links.
Others suggest that the future of carding will move to other platforms, like Telegram – although not all users trust the instant messaging service. On January 2022, a message appeared on a prominent carding forum stating that the Russian Internal Affairs Ministry had shut down the site as part of a "special law enforcement operation". While the human cost of carding and credit muling is significant, it is essential to remember that victims are not alone in their struggle.
It is heavily business-oriented, with sections dedicated to ransomware services and cyberattacks. XSS is primarily focused on hacking, corporate access, and data leaks, making it a hub for cybercriminals and hackers. Initially known as DaMaGeLaB, the forum rebranded in 2018 after the arrest of one of its administrators. While many users turn to the dark web for legitimate reasons, such as journalists or activists seeking to avoid censorship, it is also known for illegal activities. Sites on the dark web typically use .onion domain names, which add a layer of anonymity for both users and administrators.
Carding Attacks 💳: We Were Targeted, And Here’s How We Beat Them
Dark web forums, in particular, are notorious for hosting discussions on illicit topics. The seizures come less than a month after previous carding market leader UniCC announced that it was retiring along with its affiliate proxy market LuxSocks. Sky-Fraud also facilitated discussions on carding techniques and money laundering tips. This process is known as “carding”, and it has become a key part of the cybercriminal’s playbook. The data includes the service code, PIN code, and card verification code, making it highly valuable for thieves.
Torzon Market

These leaks are often sold or traded among members, contributing to the forum’s notoriety. The forum’s ability to attract new members and maintain high engagement ensures its ongoing relevance in the dark web landscape. This section supports the creation and distribution of custom hacking tools and exploits.
Performing Fraudulent Transactions
Carding can have severe consequences for businesses, including increased chargeback rates, financial loss and long-term damage to customer trust. Sources include phishing scams, infostealer malware, compromised point-of-sale systems or breached databases. Carders may also exploit weak verification systems, targeting e-commerce sites with poor fraud prevention measures in place. These attacks are fast-moving and difficult to trace, especially when businesses lack real-time fraud monitoring. When a card is verified as active, it can be used for purchases or resold in criminal networks. Most of these tactics are not bad additions to a comprehensive anti-fraud strategy.
What Makes Telegram An Attractive Platform For Cybercriminals?
It made around $4.1 million since its establishment in October 2017 according to Elliptic’s internal data. Precise figures are difficult to calculate due to Ferum’s sporadic use of a payment processor. Integrated blockchain data for every workflow. The threat actor behind the AllWorld Cards marketplace has a clear goal in mind. Some vendors even sell lists of "cardable" sites for a few dollars. Credit card prices also vary depending on the brand, with American Express being worth the most at 5.13 cents per dollar.
Greater Use Of Advanced Tools And Services
These cybercriminals use various methods, such as phishing, skimming, or hacking, to obtain credit card details. Understanding the hierarchy, reputation systems, trading platforms, security measures, and the evolving nature of these forums allows us to combat and mitigate the threats they pose. By delving into the inner workings and structure of carding forums, we gain insight into the complex ecosystem that fuels cybercrime on the dark web. Some forums even provide escrow services to ensure secure transactions, where a trusted third party temporarily holds funds until both parties are satisfied with the transaction. Trust is a scarce and valuable resource in the underground world of carding forums. Understanding the basics of carding is essential for those seeking to navigate the underground world of carding forums.



