
You can’t search for .onion sites using Google. Tor (The Onion Router) Browser is a privacy-focused web browser that routes your traffic through multiple encrypted relays across the world, ensuring anonymity. These websites use special encryption protocols and are accessible only through anonymizing tools like the Tor Browser. The Dark Web refers to hidden websites that aren’t indexed by regular search engines like Google or Bing.
Are Dark Web Browsers Safe?
Consider changing your usernames and passwords as an additional security measure. It should not be a privacy issue unless the company gets hacked or your data is exposed accidentally. If you live in the EU and want to know what data your provider has collected about you, the GDPR gives you the right to request a full report. Furthermore, end-to-end encryption—like the kind securing your WhatsApp messages—makes that data unreadable to your ISP in the first place. In most regions, laws prohibit your Internet Provider from selling your data to third parties. If that happens, you can guess what happens to your data then.
What Is The Safest Way To Access The Dark Web?
The GDPR imposes strict requirements on data controllers and processors, with substantial fines for non-compliance. In the European Union, the General Data Protection Regulation (GDPR) has influenced how personal data is handled, including on the dark web. In the United States, the Department of Justice has proposed amendments to laws like the CFAA to clarify the scope of unauthorized access and enhance penalties for repeat offenders. International collaboration is essential in enforcing laws against dark web crimes due to the global nature of these networks.
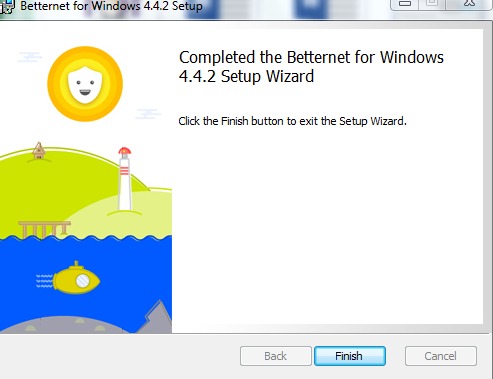
Review the info and hit Create when you’re done. For this tutorial, I’ve used Universal. It’s like in those movies where the doctors are experimenting on deadly viral strains from behind the safety of a glass enclosure.
What Is The Role Of Relays In Tor?
My advice to you would be to stick with the editor’s pick. Fortunately, in Hidden Wiki, every website is followed by a brief description so that the user knows what to expect. Well, now it’s time to fire up Tails and do a little bit of tinkering. When you’re ready, hit the Close button and you’re all set.
How To Get On The Dark Web Safely (Extensive Tutorial)
Some dark websites serve as platforms for whistleblowers to anonymously share sensitive information. However, not all the forums and social media sites are legal on the dark web and often include shocking conversations and pin boards by anonymous users. The dark web offers a marketplace section where users can buy legal or illegal products.

Does The Tor Browser Slow Down Your Speeds?
In some countries, even viewing certain types of content can be a legal risk, so you should be careful about the sites that you visit. If you’re unsure about a link, do some research or ask trusted sources within dark web communities. Be cautious of random or obscure links — these could lead to dangerous or malicious websites. Unlike the clear web, where websites are often rated or reviewed, most dark web sites are unregulated. ExpressVPN is my top recommendation for Tor VPNs because it’s fast, easy to use, and its no-logs policy has been independently audited and confirmed by third-party cybersecurity experts.
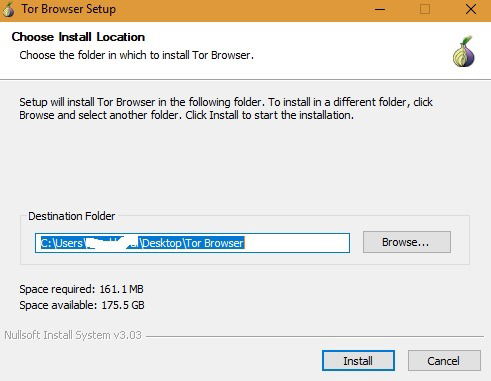
Download And Install The Tor Browser
The only benefit is that the ISP won’t know you’re using a VPN. More importantly, even the VPN service will now see what you’re doing inside Tor. However, your ISP can see that you’re using Tor because the entry node is now fully visible.

For example, the Silk Road site operator, an illegal dark web marketplace, was traced and arrested. Moreover, malicious actors can attempt phishing scams to steal your data and identity for extortion. Unfortunately, others are fake and fraudulent websites that exploit the reputation of the dark web to con people. Because of this, some people use it to get around government restrictions, while others use it for illegal activities like smuggling drugs and weapons. All in all, it is not illegal to access the dark web, but it can create issues for you. For example, perpetrators of trafficking and cyber attacks use the dark web to disguise their actions.
Words Of Caution When Using Dark Web Sites
A budget-friendly VPN service allowing users to access dark web safely anytime, anywhere, and on any number of devices they want. It offers multiple security protocols, including OpenVPN UDP/TCP, L2TP/IPSec, and PPTP. This means that there will be no data to track your activities. Moreover, NordVPN is a service that doesn’t store or log your search results.
- It hosts academic databases, private archives, and resources for journalists and human rights activists.
- It disables JavaScript and other potentially risky web features for maximum security.
- NordVPN is a highly recommended VPN for the Tor network.
- Traditional social media platforms such as Facebook have also created versions that work with the dark web to provide services across all dimensions of the World Wide Web.
- For this reason, users should be cautious when using their browsers.
Download Antivirus Software
Underneath it are deeper layers that aren’t visible through normal browsing. That said, our detailed reviews follow a strict methodology that examines all relevant performance factors to help you arrive at your own informed conclusion. Whether you’re here out of curiosity or necessity, these steps will help you browse without getting burned.
Above all, it’s vital to go on the dark web carefully and sensibly. This internet space can be dangerous, but you can safely get on it by using a VPN and then connecting to Tor. Let’s summarize the most important points from this guide on how to access the dark web.
That doesn't mean it’s impossible to track users on the dark web. Avast BreachGuard monitors the dark web for data breaches around the clock. What should you do if your information is found in a data breach or you think it’s been leaked somewhere? When data brokers get hacked, the stolen data can include compromised credit cards, social security numbers, and other data, depending on what was exposed in the breach. To check, you can use dark web scanning or breach detection tools like Avast Hack Check or LifeLock Breach Detection to search for compromised data. By monitoring known dark web marketplaces, Avast BreachGuard will alert you immediately if and when your data is found.
You could do all your browsing with Tor, though it's slower than a standard browser, something the Tor Project is working hard at to improve, says Stephanie Whited, communications director for the Tor Project. Slide up to the "safest" level, and as well as those settings, JavaScript is disabled on all sites. In "safer" mode, JavaScript is disabled on HTTP sites, some fonts are disabled, and all audio and video won't run automatically, you'll have to click to play. To review security settings, click on the onion logo in the top left and select "Security Settings", which will bring up a slider offering a choice of the default of standard, or safer and safest. The latter choice is for when access to the Tor network is blocked, and you'll be shown a variety of circumvention techniques.
You won't be able to access .onion addresses using a standard search engine as they aren't indexed by crawlers. No, as the Tor network is not good for torrenting — some Tor browsers block P2P traffic, and even Tor’s developers ask users not to use the network for P2P downloads. This encrypts your online traffic before entering the Tor network and shields your actual IP address. As well as encrypting your traffic, the Tor network changes your IP address — any site you access through Tor will only see the IP address of the exit Tor server, while your real IP address will remain hidden. All in all, Tor provides decent security and privacy, but it’s best to take precautions when using it — like using a VPN (such as ExpressVPN) to first secure your traffic before connecting to the Tor network. We strongly recommend researching your local laws to make sure it’s perfectly legal to use Tor and to only use it to access legal content.



