
Just bypass your standard web browsers and fire up your tor browser to get on the dark web to access one of the best tor sites. Most internet users love a question and answer forum like Reddit or Quora, on the surface web. They have an onion site as well, presumably to allow access to the website's content in countries that aren’t so friendly to the notorious intelligence agency's …
Are Onion Sites Safe?
- For example, you shouldn’t pirate copyrighted material, engage in terrorism, or share illegal pornography.
- Never use a personal laptop or work device for onion hosting.
- Drughub secures 10% of pharma trades—specialization rises.
- Despite Tor’s privacy-focused design, malicious entities are more likely to target your data in transit and on .onion sites.
- If you’re not using a VPN or secure browser, you’re not anonymous.
No, it is not illegal to browse the dark web. Stay safe while exploring the darknet! With Forest VPN, you can explore this intriguing world safely and securely, ensuring you remain anonymous and protected.
This is because law enforcement often actively monitors these sites. However, no matter how much you try to stick to legal websites, you can still land on illegal or highly disturbing content. For example, China uses the Great Firewall to block access to Western sites. You could be monitored closely even if you are not doing anything illegal. Moreover, malicious actors can attempt phishing scams to steal your data and identity for extortion.
Security Evolution
While the dark web offers privacy, it’s not without risks. It doesn’t log user activities, meaning your identity and actions remain your secret. Venturing into the darknet without precautions is like walking a tightrope without a safety net. Onion sites are a crucial component of the dark web. This early detection allows organizations to identify and respond to threats quickly, reducing the chances of unauthorized access, financial loss, or damage to brand reputation. Organizations need automated dark web monitoring to prevent cyberattacks.

Disable Java And ActiveX In Your Network Settings
However, the platform lacks an advanced search option and a wallet-free payment option. In 2017, the website went offline following a law enforcement action taken by the American, Canadian, and Thai authorities, but since August 2021, it’s been operational again. It was quite popular for selling a wide range of products and services. There’s also a search bar that you can use to search for any particular product or vendor. The homepage includes options like browsing products, searching, mixer, and coin exchange.
Nowadays, many people use the Tor browser to surf the public internet and navigate the deeper parts anonymously. You can quickly get into trouble for acting illegally, such as infringing on other people’s safety and freedom. Due to its anonymity, the dark web has attracted people who could endanger their lives by revealing their identities on the surface web. Simply put, accessing and browsing the dark web is perfectly legal. Overall, Subgraph OS is a secure and privacy-focused operating system well-suited for high-risk environments.
As technology changes, so has the Tor network, which has moved from anonymity to a potent marker of digital independence. You will often come across broken links, abandoning pages, and potentially harmful pages. The Tor network offer anonymity, but even more important to stay safe while on Tor is your own behavior and judgment (just like any other tool). Whether it is privacy-based tools, educational resources, or even specialty communities, the deep web has a case to the limits and restrictions of the surface. While some anonymity is present with the Tor browser, a VPN adds a second layer of protection and anonymity to your browsing experience. The Tor Browser encrypts your connection and sends your traffic through multiple layers of the network to authenticate your anonymity while using the browser from your location.
What Are Onion Links And How Do They Work?
Always keep your guard up and use reliable security tools. I feel secure knowing my data is protected.” – Jane D. Users access these sites via the Tor Browser, which conceals their identity and location. While it’s true that it hosts illegal activities, it’s also a haven for those seeking privacy from prying eyes. By leveraging automated dark web monitoring, organizations can mitigate risks, and take preventive measures before the leaked data is exploited. Manual monitoring of the dark web is inefficient and risky due to the sheer volume of data involved.
It’s a hidden collective of sites that you could only access through a special browser. Also referred to as “non-indexed” content, it’s any content hidden behind some kind of access control such as a log-in or code word. The deep web is the part of the internet you can’t access through search engines like Google and Bing.
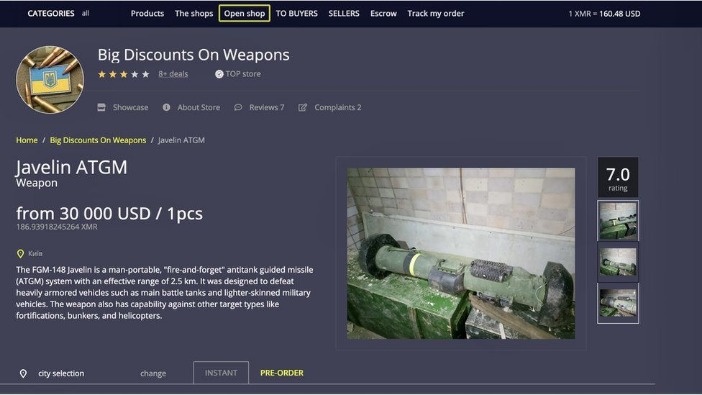
- Today, buyers and vendors look for reliable alternatives that offer security, escrow protection, and a strong vendor community.
- Tor is among the best private browsers for anonymous communications and internet freedom.
- It is a specific Debian-based version of Linux software that leaves no traces of the user activity or the operating system on the computer.
- PGP encryption protects sensitive communications including shipping addresses from market administrators and potential attackers.
- Some content can be unmoderated, though, so it’s worthwhile to be careful while using this platform.
Best Dark Web Websites: Video
Dark web links can change frequently, so always verify addresses from multiple trusted sources before visiting any .onion site. Always exercise extreme caution and verify the legality of any services you access. Cryptocurrency miners and other malicious software often target dark web users. Using Tails OS can further security, as all your data is reset every time you close the device. The dark web contains numerous security risks, from malware to scams and illegal content.
Acronis Cyber Protect Cloud: New Version C2505
It relies on P2P connections and requires specialized tools and software. Lastly, the dark web is the portion of the deep web that is generally inaccessible and is much larger than the surface web. As a result, you cannot find them with a regular search engine.
Registration was mandatory to access the Silk Road (like most darknet platforms). All the payments were made through cryptocurrency, further enhancing marketplace anonymity. However, you must wait some time to reassess this marketplace because it’s been shut down. The Torrez market is one of the biggest dark net marketplaces, also called a community-driven marketplace. Like other marketplaces, ASAP Market also requires you to register for an account.
Always remember that while the above measures significantly reduce risks, no method guarantees complete security on the dark web. This isolates any potential malware and prevents cross-contamination with your personal data. Create new anonymous accounts when necessary, using temporary email services. Avoid entering any real personal details or using existing accounts on dark web sites.
You need to ensure you’re only accessing reliable dark web sites, and the ones listed below are among the safest ones that currently work. You’ll also find essential safety tips for exploring this hidden part of the internet. After extensively testing many dark web sites, I’ve made this guide to cover the most reliable dark web links across different categories.
It includes private corporate sites, paywalled sites, health providers, and lots more. It simply accounts for the vast unindexed content online, raw data that Google doesn’t know about and doesn’t care about. The Deep Web is not a place that is not hidden and consists of zero criminal activity. The media usually describes the Deep Web as a vast hidden area five thousand times larger than the surface web and loaded with criminals, but that is false. The clear or surface web is the part that is open to indexing for search engines such as Google. The term dark web comes up many new stories and articles discussing ransomware and other cyberattacks, often alongside the deep web.

Secure markets collect minimal user data and delete information after transactions complete. Law enforcement and competitors frequently launch DDoS attacks against darknet markets. Top markets implement secure session management, mandatory two-factor authentication, and automatic logout after inactivity. The most secure markets address all these vulnerability categories through comprehensive security programs. Understanding common vulnerabilities helps users evaluate market security. Security represents the most critical factor when selecting a darknet marketplace.
Some of the best-known names include Abacus Market, Russian Market, and BriansClub, all with thousands of illegal items available.Despite closures by authorities or the typical “exit scams” (when a marketplace disappears with all the money), these sites continue to pop up. The dark web is a hidden division of the internet that can only be accessed by those with special tools and is concealed below regular browsing. Developers, journalists, educators, and advocates for privacy use onion sites as a means to share information in a way that is free and secure. Exploring the deep web responsibly requires a clear understanding of the potential it offers and being aware of its limitations—staying anonymous, not clicking suspicious links, and using verified tor sites from written onion site lists. Verified onion site lists insure that each tor link you visit is active, secured and legit, enabling you to explore darknet resources confidently. To ensure you can navigate this complex network of sites with ease and don't waste time on outdated tor links, you can rely on verified lists of onion sites.
Whereas the deep web is the part of the web not searchable by traditional search engines and requires special tools to access it. Some markets even sell privacy tools, but you are more likely to run across counterfeit prescription pills and stolen identities. The anonymity provided by onion routing comes at the cost of slowing your internet considerably. With the onion browser, you can access ordinary HTTPS websites on the web.



