I review privacy tools like hardware security keys, password managers, private messaging apps, and ad-blocking software. Signal is our Editors’ Choice for private messaging apps because it does a great job of blending privacy and social media functionality for a highly customizable chat experience. Once you’re in, continue to use caution to protect your anonymity and safety.
Unraveling The Truth About The NIST’s New Password Guidelines
Even if they aren’t actively malicious, they might still have weak security or expose you to threats. The Tor Browser is the safest and most trusted way to access the dark web. By following some basic security tips and using the right tools, you can greatly reduce your chances of running into trouble. While the dark web comes with risks, it’s possible to explore safely if you take the right precautions. You can download the VPN app from the provider’s official website or your device’s app store.
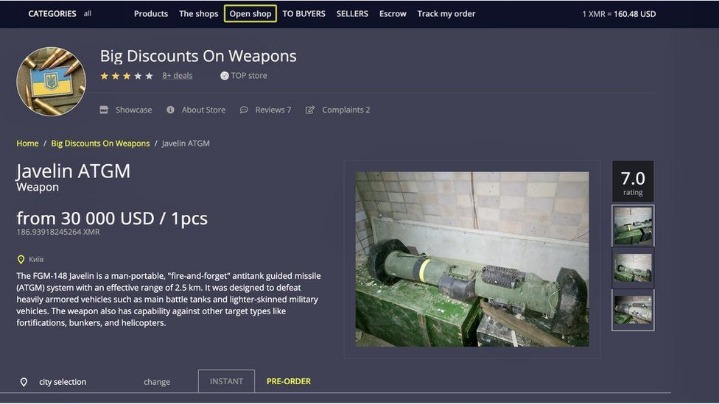
And that's why organisations such as the CIA, the New York Times and Facebook have onion versions. That central control allows for censorship, as by interrupting that lookup a site can effectively be banned from the web — this is why Turkish protesters were spraypainting IP addresses on walls in 2014, to tell others how to access Google directly without going via a DNS server. The dark web is infamous as a dangerous place, where drugs are bought and hitmen hired, but it can be a safe way to browse the internet if your privacy is serious concern. Gannicus Oliver is an experienced tech journalist (he loves writing on emerging techs and digital privacy issues) and an online business consultant.
Stay Safe

For example, Briar is an extremely private chat app designed to help journalists communicate anonymously with sources. The second, less secure option is to use encrypted messaging apps with ties to specific non-profit or activist organizations. If you want to observe the lawless sides of the internet from afar, check out YouTube videos of dark web explorations, like this one from John Hammond, to satisfy your curiosity. I don’t recommend seeking out dark web content unless you have a specific reason to do so. Remember to update the Tor Browser regularly to ensure you have the latest security patches, and scan your computer for malware regularly using antivirus software.
Many popular websites, such as Facebook and DuckDuckGo, have Onion versions, so check if yours has one. For example, in Safer mode, JavaScript is turned off on non-HTTPS (insecure) sites, but in Safest mode, JavaScript is turned off entirely for all sites. If you’re having trouble accessing a website via Tor, it could be that a node, especially the exit node, has a problem connecting to the site. The tradeoff is that you don’t get personalized search results, as DuckDuckGo doesn’t collect user data. Others outrightly block Tor users from accessing their platform, so you might not be able to open some popular platforms. To surf the web privately, you need to connect to the Tor network from your browser.
Is It Legal To Access The Deep Web?
This encrypts your internet traffic using your VPN’s servers, protecting against outside parties monitoring all of your device’s internet activities. A secure VPN server slows down your browsing much less than the Tor Browser and also opens access to geo-blocked local content around the globe. This encryption and relaying of your browsing data prevents anyone who is watching from detecting which websites you are visiting.
How Do Onion Routing And Tor Work?
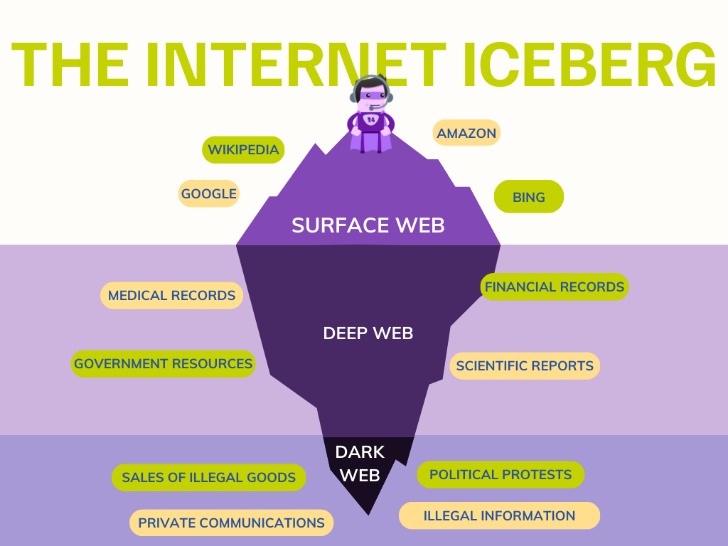
This part of the internet is notorious for illegal activities, facilitated by the anonymity it offers. It's a place where you'll find data leaks and illegal trades, but also legitimate, legal online activities users want to carry out without attracting the attention of law enforcement agencies or governments. The Tor tab funnels traffic through the Tor network, heightening anonymity during sensitive browsing sessions. The Tor routing innovations created for US intelligence agents are now used by a variety of everyday users who value their online privacy and data security. This elaborate process shows how secure Tor is at protecting data and hiding your IP address from websites, your ISP, and even the government. A VPN provides you with anonymity by creating a private network from a public internet connection.
- A VPN combined with Tor provides better anonymity.
- However, since it is so popular, you will find several versions of the program on the internet.
- A VPN is a confusing factor for many because there are two ways to use it with Tor.
- It doesn’t reach the same level of anonymity as the full Tor Browser, but it’s much easier to use, especially if you want something fast and functional.
Accessing On Android
- And before you dive in, we’ll explain how to use Tor to access the dark web.
- While the Tor Browser does an excellent job of protecting your privacy and anonymity, you really shouldn’t use it as your daily driver browser.
- Another vital precaution is to ensure that your .onion URLs are correct.
- In fact, it’s been endorsed by none other than Edward Snowden, a U.S. technology consultant known for exposing global surveillance programs—so that says a lot about its focus on security.
- While Tor itself encrypts traffic within its network, the connection between the user’s device and the first Tor node (the entry node) is visible to the ISP.
If you use the Tor browser to access a standard website, it offers protection and anonymity to users — they pop into the Tor cloud, that "onion space", and pop back out virtually elsewhere, with their identity and location obscured. When people go on about the so-called dark web, they're usually talking about onion sites, which aren't searchable via Google or accessible via standard browsers. Tor refers to "the onion router", which is a network that bounces your traffic through random nodes, wrapping it in encryption each time, making it difficult to track; it's managed and accessed via the Tor browser. The internet providers and websites can still see that you’re using Tor, as Tor node IPs are public.
Added Security: Use A VPN
"If the site invests in setting up a 'native' Tor onion-address for their website, then people who use the Tor browser to access that address never step outside the protection of the Tor cloud," Muffett says. "The Tor network is another network which sits on top of the TCP/IP internet, stitching the participating computers together into a wholly new network 'space', not IPv4, not IPv6, but 'Onion Space'." That may seem an extreme way to browse the web, but such protections are increasingly worth considering, says Sarah Jamie Lewis, executive director of the Open Privacy Research Society. The spy agency is hoping to securely and anonymously collect tips, though its entire website, including job listings, are available on the onion service. Naval Research Laboratory to protect sensitive government communications.
The users of the dark web are typically aiming to block governments from snooping on them. Absolutely no one knows who’s surfing on the dark web, who is selling, who is buying or anything like that – as long as you take the correct safety and online privacy precautions. For example, the URL of Silk Road is rather unintelligible and may look something like “gan4arvj452janndj4a76.onion”. While I know that none of my readers are looking to engage in any of the activities I’ve mentioned, I felt that it was important for my readers to be aware of the dangers that lurk on the dark web. To access the dark web, you’ll need a specific set of tools – more about that later in the step-by-step section. Their research estimated the size of the deep web to be around 7.5 petabytes.
How To Access The Dark Web Safely: A Step-by-step Guide
If you live in a regime that blocks Tor or need to access a web service that blocks Tor, you can also configure Tor Browser to use bridges. These services look at your IP address and guesstimate your country and language, but when using Tor, you will often appear to be in a physical location halfway around the world. Tor Browser connects at random to one of the publicly listed entry nodes, bounces that traffic through a randomly selected middle relay, and finally spits out your traffic through the third and final exit node. As the images below illustrate, Tor consists of a three-layer proxy, like layers of an onion (hence Tor’s onion logo). If a site you normally visit suddenly returns 404 when visiting over Tor, the service is likely blocking Tor traffic and being needlessly opaque about it. Still, Tor has gotten quite a bit faster over the years, and with a good internet connection, you can even watch YouTube videos over Tor.
Use Encrypted Communication Apps
Tor is also useful for bypassing content that is otherwise restricted to you. Edward Snowden famously used the Tor network to leak details of the US government's mass civilian surveillance program to the press. If you want to explore the internet without leaving a footprint behind, Tor is the browser for you.