Cybersecurity researchers have uncovered a dangerous tool causing a stir on the dark web and within And if you ever feel the need to quickly "disappear," just tap the “Fire Button”—it instantly wipes all your tabs and browsing data. That said, it’s a more technical option, best suited for those who want to build or participate in networks beyond the reach of traditional surveillance. GNUnet isn’t just a browser—it’s more of a platform for building decentralized networks. It doesn’t reach the same level of anonymity as the full Tor Browser, but it’s much easier to use, especially if you want something fast and functional.
Ransomware, which encrypts a user’s files and demands a ransom for their release, and keyloggers, which record keystrokes to steal passwords and other sensitive data, are among the types of threats commonly found on the dark web. The dark web serves as a common platform for cybercriminals to distribute various types of malicious software designed to compromise users’ devices and steal their personal information. Users should be well aware of these risks before venturing into this part of the internet. Taking these precautions can significantly enhance a user’s safety and privacy while accessing the dark web using Tor Browser.
Don’t Download Unrecognized Files
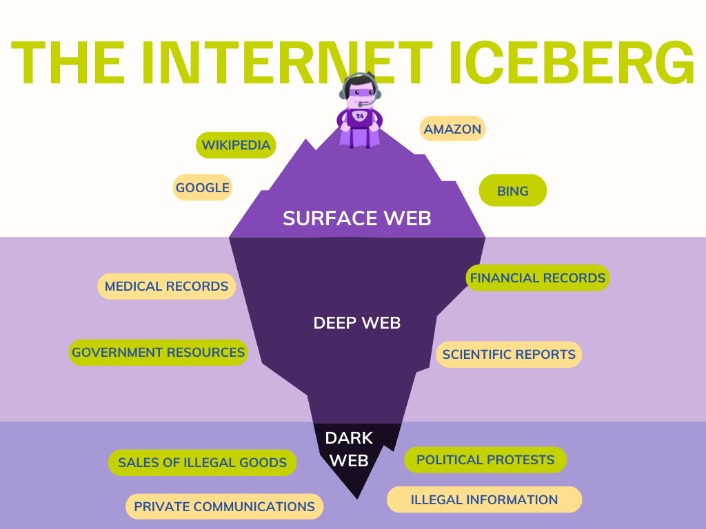
You might’ve heard of the domain extension called “.onion“, which sits at the end of each dark web website. You can go on the dark web safely, use legal sites, and enjoy the experience without worries. Relying on Tor to keep you anonymous online is a good recipe for disaster; you’ll learn why. We know what you’re thinking, or some of you. The so-called surface web is readily accessible to all of us and less interesting.

Should I Only Use A VPN To Access The Dark Web?
Only a tiny portion of the internet is accessible through a standard web browser—generally known as the “clear web”. Start by downloading the Tor browser, which is necessary to access dark web sites. The dark web is a part of the internet that isn’t indexed by search engines. The Tor browser offers strong online protection, given that it routes your online traffic via severa…
Exposure To Illegal Content
As such, the dark web has attracted many parties who would otherwise be endangered by revealing their identities online. Understanding that the nature of the internet meant a lack of privacy, an early version of Tor was created to hide spy communications. In other words, the deep web covers everything under the surface that's still accessible with the right software, including the dark web. At the dark end of the web, you’ll find the more hazardous content and activity. Without visible links, these pages are more hidden for various reasons.
Wide Area Network (WAN): Definition, Examples, And Technologies
Everything you can find with a Google search is part of the surface web. It’s where scammers and bad actors buy and sell leaked confidential information, like credit card information, email addresses, and in some cases, home addresses, too. As previously mentioned, the dark web is commonly used for illegal trade. You can only access the dark web with the Tor browser, which prevents tracking, surveillence, and ad targeting. Let’s dive in to clear up what exactly the dark web is (and what it isn’t) and how it’s different to the web you know.

Download Tor Browser
The “Onion Browser” is available in the App Store. Go to the directory where you downloaded the Tor Browser installation file. Go to the directory where you saved the downloaded Tor Browser installation file. When the final layer of the “onion” is reached and decrypted, the message arrives at its destination. Each of these nodes removes or “peels” away a single layer, which uncovers the data’s next node destination. The Tor Browser is configured to make all users look the same, making it nearly impossible for users to be fingerprinted based on their browser and device information.
This way, you can protect yourself from websites that want to steal your login details or cryptocurrency. Although it’s no longer active, it’s setting the standard for coming onion links. The biggest and most frustrating part about dark websites is that they live for a short span of time.
Naval Research Laboratory to protect sensitive government communications. Also, it contains several illegal goods, stolen data, credit cards, and more. It was known for facilitating the sale of illegal drugs, goods, and services using Bitcoin cryptocurrency. Deep down, the tip of the iceberg is where over 90% of the internet content is. This (practically) irreversible process highlights the importance of taking preventive measures by utilizing a service that monitors your data for potential breaches. Also, your data is more likely on the deep internet in one way or the other.
Step 3: Connect To The Tor Network
It’s extremely capable at hiding your IP address from traffic analysis or network surveillance. Remember, the deep web is any part of the internet not indexed by search engines. There are still ways to get to it, especially for hackers, but it’s not easily accessed without the proper permissions. Most of the internet is made up of these behind the scenes content.
Implement dark web monitoring, block Tor exit nodes, conduct security audits, and educate employees on threats. Potential risks include malware infections, exposure to illegal content, and surveillance by authorities. Whistleblowing, bypassing censorship, private communication, and secure research are all valid reasons. They use it to investigate leaks, gather threat intelligence, and access hidden forums legally. Onion routing is the process of encrypting and routing data through multiple layers (nodes) to ensure anonymity.
Connecting To A VPN Server
- For example, you can use Signal as your daily messaging app– it has end-to-end encryption and collects minimal data unlike many other messaging apps.
- But be warned, it's not as user-friendly as the typical clearnet websites you access.
- What’s more, law enforcement agencies monitor dark web activities.
- The browser isolates each website you visit, so it prevents trackers and ads from following you online.
- For example, the BBC website is not accessible in such countries.
In addition, it ensures that no record of communication is stored. This makes it even harder for third parties to see your email traffic. However, note that the site only uses non-sensitive and public data for the metrics. This service is a good source of statistics if you have a school project requiring research on Tor and the dark web. For example, the BBC website is not accessible in such countries. After all, it enables users to connect and communicate with each other from around the world.
Accessing hidden layers of the internet can be fascinating and useful, especially regarding privacy and information security. Tor over VPN means you connect to a VPN first, then open the Tor Browser, so your internet traffic is encrypted by the VPN before it enters the Tor network. The dark web is just a part of the internet that isn’t indexed by traditional search engines and requires special software like the Tor Browser to access. To reduce the risk of these threats, it’s highly recommended to disable JavaScript when browsing dark web sites. JavaScript is a programming language used by websites to add interactive features, such as videos, forms, and dynamic content. Because Tor over VPN puts your privacy in the hands of the VPN provider, it’s important to choose one with a strict no-logs policy, meaning it doesn’t store user data.
Federal Criminal Defense
While you can’t install the Tor browser from the official website, Chromebook users can configure it via a few simple Linux commands. Aside from the potential for illegal actions, certain countries, such as China, Iran, and Russia, have banned it completely. The installation, however, is a different story, and we have already covered it for all known operating systems in this article above.
You can search for Tor’s hidden services on your normal browser through a search engine such as Ahmia. Tor's hidden services have .onion domain names, which is why some people call Tor “the onion browser.” Tor’s hidden services, also known as onion services, keep the publisher of the service anonymous. On normal browsers, the IP address of your computer or router can be traced as you access websites. Dark websites are encrypted behind relay nodes as well, so neither the visitor nor the host of a website know each other’s identity.
How To Install The Tor Browser On All Linux-based Devices
The Deep Web isn’t some mysterious underworld—it’s actually a huge part of the internet that you use every day without even know… Think of the dark web as a hidden neighborhood on the internet. Other tools that people use include encrypted email, such as ProtonMail, and more advanced users may consider secure operating systems such as Tails. You don’t go to Google or another normal search engine to find sites on the dark web. That’s why users have to look for links on “dark web aggregate” sites or wikis where darknet admins and users shared links for others to use. Just like with any application, to access the dark web, you must go through an overlay network, in this case, Tor, the most popular overlay protocol.