“I have been a single mother since they were 2 and 3 years old, and I dedicated myself to raising them, and I didn’t have my own life for a long time. They began an intense online relationship during which he asked her for financial help. Besides losing her nest egg, Weber said she had borrowed money against her home, which had been paid off. When she alerted authorities, they told her, “ ‘You’re not going to get your money back,’ ” she recalled.
DeFi offers extra privacy and lighter oversight, letting users bypass KYC checks and other red tape, which makes it a convenient way for criminals to cash out quietly. While CEXs still play a major role in the crypto sales cycle, DeFi is now a rising alternative. His charges include a wide range of cyber and financial crimes.
The Role Of Crypto Anonymity Tools
This sharp decline in activity mirrored warning signs observed in previous darknet market exit scams, where operators initially downplay technical difficulties before vanishing altogether. As of now, Empire appears to be the only major darknet market accepting Monero, but that could change in 2020. Monero uses an obfuscated public ledger to make it more difficult to see the senders, receivers, or amounts of cryptocurrency exchanged on transactions. OpenBazaar, for instance, only has between 10 and 20 vendors with substantial traction, while the most popular markets have hundreds. Instead, they receive a new disposable wallet for every order they place, and the cryptocurrency they deposit goes straight to the vendor — the market itself never actually controls it.
Dominant Markets
Convert and track cryptocurrency rates for darknet trading. 80% of top markets now use escrow networks, up from 60% in 2023. Multi-crypto markets and 2FA define the top 10—see markets.
Despite losing its Estonian license to provide virtual currency services following the Estonian Financial Intelligence Unit’s investigation, Garantex continues to provide services to customers through unscrupulous means. This is the second time in the last six months that Treasury has partnered with the Estonian government in relation to a virtual currency exchange facilitating malicious cyber activity. In February 2022, Garantex lost its license to provide virtual currency services after supervision by Estonia’s Financial Intelligence Unit revealed critical AML/CFT deficiencies and found connections between Garantex and wallets used for criminal activity.
Beyond Bug Bounties: How Private Researchers Are Taking Down Ransomware Operations
Locating the correct .onion address for a darknet market is the most critical step for secure access. The selection of a darknet market is a primary determinant of transaction success and user safety. Platforms like the Nexus darknet market provide reliable access through official links and onion mirrors.
Scammers and other launderers of cryptocurrency often move illicit assets between numerous anonymous addresses before depositing the funds at an established exchange. But Pamela Clegg, a longtime blockchain investigator who has done work for crypto firms and banks, said the exchanges often take a more casual, less scientific approach to assessing suspicious transactions than banks do. She sent payments, first through remittance services like Western Union and World Remit, then to cryptocurrency wallet addresses he supplied. It landed in cryptocurrency wallets that sent most of their funds on to two OKX deposit accounts, according to an ICIJ analysis of the wallet addresses Weber sent money to. Operation Destabilise was a rare triumph for law enforcement in the fight against cryptocurrency-related crime. “What we have seen is that these networks have heavy exposure to market-leading crypto exchanges,” said a U.K.

Russia’s ‘Kraken’ Darknet Market Crypto Sales Soar 68% As Global Trade Falls
The darknet includes networks like Tor, I2P, and Freenet that provide anonymity for users. Dark markets continually adapt and evolve to stay ahead of law enforcement and security measures. Transactions within dark markets predominantly involve cryptocurrencies like Bitcoin, Monero, or Ethereum. To access darknets, users typically need to download and configure the Tor Browser; a modified version of Mozilla Firefox that routes all traffic through the Tor network. Emphasizing anonymity, darknets and dark markets operate on a technical level that significantly differs from the conventional surface web.
Agentic AI-Powered, Intelligence-Driven Unified Cybersecurity Platform
These results suggests that a strong dominance in the ecosystem induces anticorrelation between the median net income of sellers and buyers. Specifically, sellers show a trend of increase and buyers a trend of decrease in their median net income before the shutdown. This structural change is reflected in the median net income of sellers and buyers, as shown in Fig. After the shutdown of Silk Road, in the last quarter of 2013, the ecosystem evolves to a structure where several markets coexist. Structural change in the ecosystem by dominant markets. Three markets consistently sustain over 60 percent market share, namely Silk Road, AlphaBay, and Hydra.
What Are The Risks Of Using Dark Markets?
All of that means Telegram's takedowns are by no means the end of the crypto-scam industry, says Robinson. Huione Guarantee's parent company, the Cambodian financial conglomerate Huione Group, includes a company linked to the family of Cambodia’s prime minister, Hun Manet. Tudou Guarantee has already seen a significant surge in new users, Robinson says. Elliptic says that Haowang Guarantee's owners also own a stake in another similar Telegram-based market called Tudou Guarantee, according to a Telegram post from one of Haowang's administrators, and they may seek to rebuild their business there.
Stolen Data And Identity Theft
Still, investigators have not ruled out the possibility of a hidden law enforcement operation. TRM Labs stated that the recent rise in new users may have attracted more attention from authorities. The site’s administrator, known as "Vito", told users this was due to too many new accounts and a denial-of-service attack. At the end of June, customers began reporting that they were unable to withdraw their money. Aside from his work, Danish enjoys spending his time on the football field. Radar Rundown Free firewall software allow privacy ethusuiasts to secure their network and block mal…
- Furthermore, law enforcement worldwide has stepped up its efforts, seized assets, and disrupted key money laundering networks.
- Thanks to the evidence Stefan and his team gathered on the Robertsson brothers, Swedish courts were able to convict them of selling drugs on the darknet.
- Discover everything about what is a darknet market, how it works, security threats related to it, and learn how to protect your data online.
- They employ various techniques, such as tracking and infiltrating dark markets, developing advanced threat intelligence, and enhancing international cooperation.
- A once-sizable illicit enterprise that began in 2014, AlphaBay was closed by authorities in 2017 and then reopened in 2021.
A study based on a combination of listing scrapes and feedback to estimate sales volume by researchers at Carnegie Mellon University captured some of the best data. It estimated a quarter of all purchases were for resale and that the trend towards decentralization meant they are unlikely to be eliminated any time soon. Professor for addiction research Heino Stöver notes that the shops can be seen as a political statement, advancing drug legalization "from below".
Jardine also emphasized the importance of using services that actively emphasize security in the decentralized finance space. These types of scams more than doubled in revenue year-over-year, with data indicating a growth of 85x since 2020. Although scams remain one of the biggest drivers of crypto-based crime, with $4.6 billion in revenue for 2023, the figure was down from the previous year’s $5.9 billion.


Regulatory countermeasures, including blockchain analytics and the FATF’s Travel Rule, aim to trace illicit flows. These methods exploit gaps in compliance frameworks, complicating efforts to track and prevent financial crimes. Crypto anonymity tools, such as mixing services (tumblers) and privacy coins, enhance transaction privacy by obscuring the origin of funds. The methods take advantage of the pseudonymous nature of cryptocurrencies and evolve constantly to remain one step ahead of regulatory monitoring and blockchain analytics. Nevertheless, finding the perfect balance between financial secrecy and regulatory needs is a future challenge for digital finance.
Individuals began using the darknet to pseudonymously sell illegal content without face-to-face interaction. Given the darknet’s infrastructure, which is hidden behind onion routing, the darknet attracts sites whose proprietors want to remain anonymous. There are certain sites on the darknet (and on clearnet) which attempt to manually track and publish sites on the darknet, but common browsers do not link directly to darknet. DNMs are located on the “darknet,” which is unreachable on standard internet browsers like Chrome, Firefox, or Safari because the darknet is unindexed. See how leading agencies and organizations are disrupting crypto crime with blockchain intelligence Striking a balance between regulatory control, user privacy, and technological progress is essential for a secure, inclusive digital financial future.
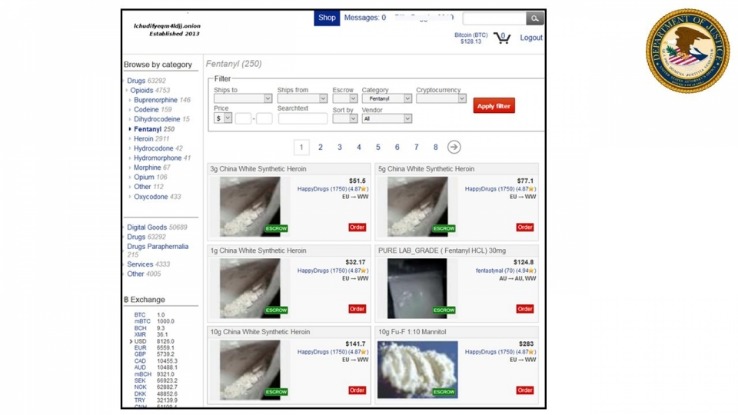
- Department of Justice announced the results of Operation RapTor—an unprecedented international crackdown on darknet narcotics trafficking.
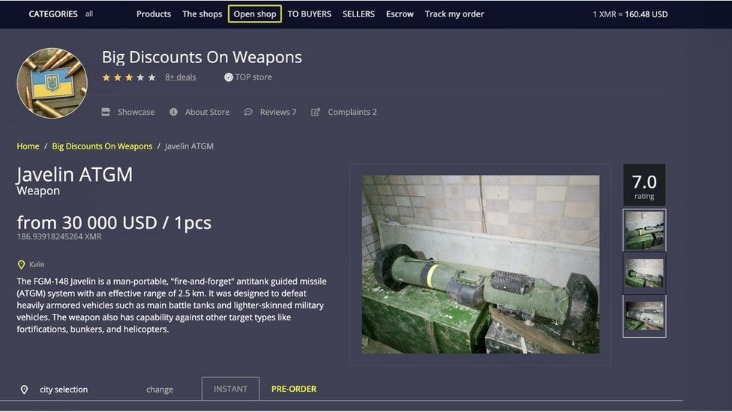
- Some marketplaces have even mandated Monero-only transactions, underscoring a strong preference for privacy-focused coins over traceable ones.
- From the rise of crypto-fueled markets to AI-augmented cybercrime, the numbers paint a vivid picture of a space that’s expanding faster than most can monitor.
- “The Biden administration’s war on crypto is over,” declared Karoline Leavitt.
- Blacksprut, which rose to prominence with Mega in the wake of Hydra’s 2022 sanctions designation, law enforcement seizure, and subsequent collapse, came in third with 13.6% less revenue YoY.
- It’s a place where illegal activities such as selling credit card numbers, bank login details, weapons, hacked social media accounts, and drugs take place.
The use of digital signatures can also help verify the authenticity of users and transactions. These digital currencies provide a degree of anonymity, as transactions are recorded on a public ledger but do not directly link users to their real-world identities. Darknets rely heavily on Tor (The Onion Router), a privacy-focused network designed to conceal users’ identities and locations. They employ various techniques, such as tracking and infiltrating dark markets, developing advanced threat intelligence, and enhancing international cooperation. These hidden networks provide a platform for illegal activities that include the sale of stolen data, hacking tools, weapons, counterfeit currency, and narcotics. Today, darknets are populated by a vast array of users, ranging from privacy-conscious individuals to cybercriminals, hacktivists, and nation-state actors.
The report also revealed that despite a likely record year for overall crypto crime revenue, inflows to darknet markets and fraud shops declined in 2024. Dark web marketplaces are hidden online bazaars on Tor or similar networks where anonymous vendors sell illicit goods. TRM Labs noted that such enforcement crackdowns historically destabilize the darknet market landscape, with displaced users flocking to the next prominent marketplace. Abacus Market, one of the most influential Bitcoin-enabled darknet marketplaces in recent years, has reportedly vanished without warning, fueling widespread suspicions of an exit scam.