If a breach is detected, BreachGuard will notify you right away and help you take the steps you need to secure your data immediately. Avast BreachGuard monitors the dark web for data breaches around the clock. What should you do if your information is found in a data breach or you think it’s been leaked somewhere? When data brokers get hacked, the stolen data can include compromised credit cards, social security numbers, and other data, depending on what was exposed in the breach. To check, you can use dark web scanning or breach detection tools like Avast Hack Check or LifeLock Breach Detection to search for compromised data.
Dark Web Sites Offering Educational Resources
LeakLooker indexes live and historical data leaks found on underground forums, often used to identify early data breach activity. Yes, platforms like DeHashed, LeakLooker, and DeepPaste provide access to data breaches and leaked credentials. SecureDrop is a secure platform used by journalists and whistleblowers to anonymously share sensitive information via the dark web. Onion.live is a platform that tracks the status of dark web sites and provides trust ratings to help users verify site legitimacy. Dread is a Reddit-like forum on the dark web where users discuss cybersecurity, marketplaces, tools, and underground activities.
By providing free access to scholarly literature, Sci-Hub aims to facilitate scientific innovation, research, and education. The platform operates under the belief that scientific knowledge should be freely accessible to all, challenging the traditional academic publishing model where key research findings are often locked behind high subscription fees. The core mission of Sci-Hub is to remove barriers to scientific knowledge and democratize access to academic research. Once a submission is made, journalists can access the data using decryption keys, ensuring that only authorized personnel can view the information. SecureDrop operates by hosting a physical or virtual server at the media organization's premises, which sources can access via the Tor network.
What You Need To Securely Browse The Dark Web
Even though it’s a “Porn” forum, it explicitly mentions the content being “legal” so accessing the site won’t necessarily land you in jail. Sinbox is another one of the legal Tor links providing free, anonymous, encrypted and secure Emailing platform. No registration, privacy details are asked for, it’s more like an FTP-directory where you simply click on links to download/view the mangas. It’s here on this list of legal Tor links because it’s completely legal, and actually works towards helping users quit or reduce drug-intake. One of the best uses the onion network could be put to, SecureDrop is one of those legal Tor links which lets people expose corruption in govt.
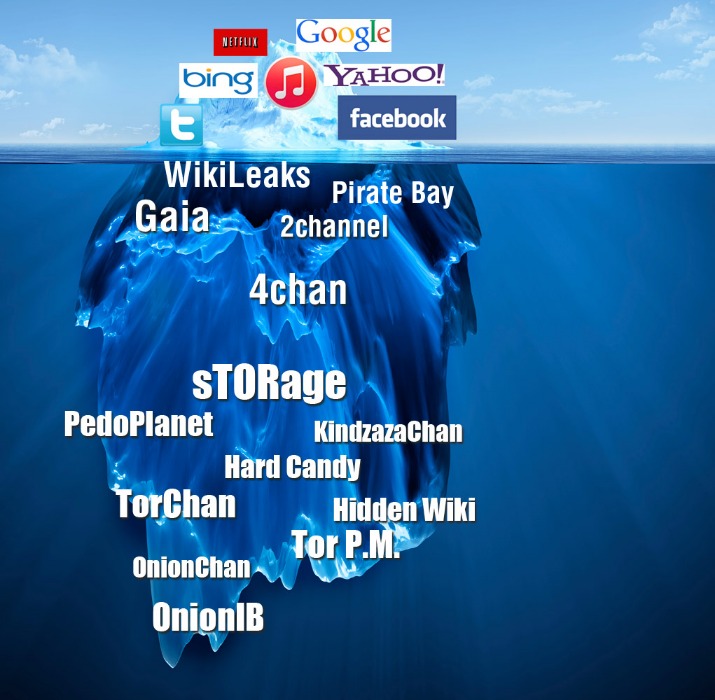
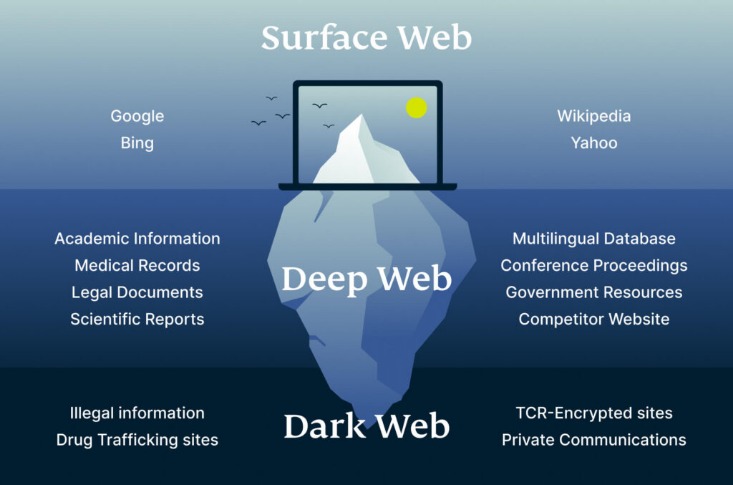
Then, a part of the deep web is the dark web which is only accessible through special software and tools. Some of the deep web sites also use unusual TLDs like .gov, .com, or .net, which normal browsing engines will fail to track down. Furthermore, logging in or from one’s specific IP address or URL is necessary to access such deep web information. It includes sites such as Facebook, Wikipedia, online commerce sites, and YouTube, among others. Anyone and everybody can access it without any setup.
Websites that are up and running cannot carry out all tasks automatically. Most important of all, there are the web administrators. As an investigator or a casual user with investigative mind, what makes a person allured into dark web?
Easily initiate data encryption on your external drives and disks, ensuring compliance with your specific company policies. Venturing into the dark web highlights the need for robust data protection, not just for online activity, but also for your portable data. The dual nature of the dark web—as both a haven for privacy and a platform for crime—perfectly illustrates the complex ethical and security challenges it presents.
What’s The Difference Between Tor And VPN?
The Escrow’s .onion link provides a platform for conducting anonymous transactions on the Dark Web by holding funds securely until agreements are fulfilled. It is a popular tool for journalists, researchers, and users who need to document online content. It filters out harmful and illegal content, focusing on legitimate resources and services. SecureDrop’s .onion link is a platform designed for whistleblowers to securely and anonymously submit sensitive information to journalists.
- The chances of monitoring the original poster are also very good.
- There are many places in the world where access to international news sources is blocked.
- These are the top 10 dark web search engines that allow easier access to the hidden corners of the internet.
- The service remains free to use, and the secure design prevents access to third parties, eavesdroppers, and other malicious agents.
- Data breaches happen all the time, and your login credentials and other data might be on the dark web already.
- A VPN provides strong security for everyday browsing without the extra delays, middle checkpoint, and then finally the exit gate.
SecureDrop is an open-source platform that facilitates secure communication between whistleblowers and journalists. It’s particularly useful for journalists, whistleblowers, and those who urgently need to send or receive confidential data. Insights like these help researchers and advocates understand how and why Tor is being used. Tor Metrics highlights that about 22% of daily Tor users come from Russia, while the USA ranks second at 15%. It’s an interesting resource that translates Tor internet traffic levels into easy-to-digest stats.
Dangerous Software
The dark web is a mysterious place that can only be accessed with specific tools and services. Plus, it’s slower since your data travels through the same four steps – entry node, relay node, exit node, and then the VPN server. By connecting to a VPN before using Tor, you mask your real IP address before it reaches this entry node, adding an extra layer of security and anonymity. Your activities on the dark web are not entirely shielded from tracking, and relying solely on anonymity can lead to a false sense of security. Using common sense like avoiding clicking on shady links or download buttons, sticking to known sites and adding a VPN for an extra layer of protection, you should be fine.
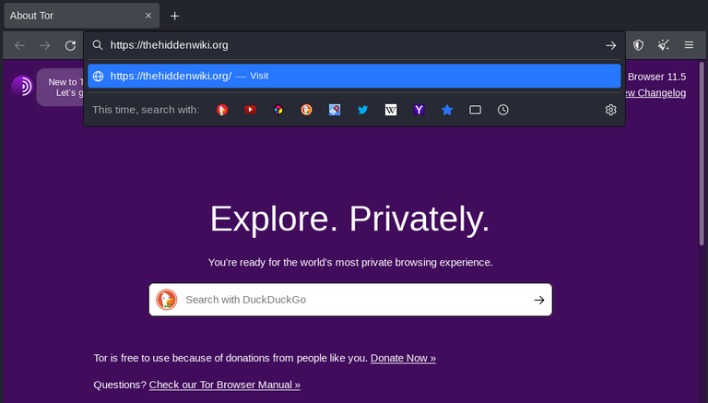
How Do I Access Onion Sites?
Many users make the mistake of using personal information out of habit, something that can instantly defeat the purpose of using the dark web in the first place. On the dark web, appearance can be deceiving, and often, it’s designed that way on purpose. Some are so well-built that they appear trustworthy until it’s too late.
Roundup – Best VPNs For Speed
For example, you shouldn’t pirate copyrighted material, engage in terrorism, or share illegal pornography. Remember that illegal activities can still incriminate you, whether you are using a Tor browser. You can quickly get into trouble for acting illegally, such as infringing on other people’s safety and freedom. Due to its anonymity, the dark web has attracted people who could endanger their lives by revealing their identities on the surface web.

Image Hosting — Upload & Share Images
Since the organization behind it is independent, it’s fully user-supported and relies on donations to keep its site up and running. Riseup provides email and chat services that keep no record of your online activity. Accessing ProPublica via the Tor Browser gives users an added layer of privacy and lets them bypass restrictive government censorship. However, Ahmia doesn’t have a large developer supporting it, so it’s been the target of scams or cyberattacks in the past.
In some cases, it’s also used for private messaging, cybersecurity training, whistleblowing, and other legitimate uses. Dark web browsers and search engines do a lot of work to mask user identities, but you’re never completely untraceable. Typically, you can find dark web URLs through forums, databases, or by talking to others who frequent those sites. DuckDuckGo is built into the Tor browser, making it a convenient option for looking up dark web websites.
Data breaches happen all the time, and your login credentials and other data might be on the dark web already. The Tor network allowed safe communication channels for political dissidents and American intelligence operatives around the world. Cybersecurity teams comb through these breaches and incorporate their findings into their security software, helping people like you. If found, take immediate steps to secure your accounts and personal information. Your information might be on the dark web if it was exposed in a data breach, sold, or stolen by hackers.



