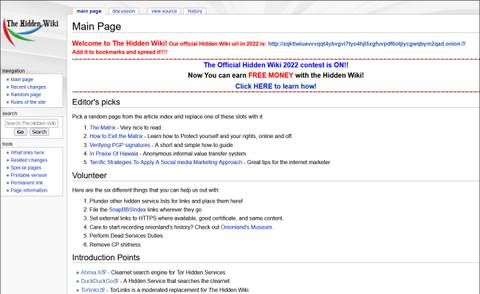
The “Hidden Wiki” (which can be accessed in a normal browser) offers a large collection of dark web links, but be careful, as many of those links are to dangerous websites. The dark web (often referred to as the “dark net”, “black web”, or “black net”) is a small section of the deep web that is hidden and kept inaccessible to regular internet users on purpose. The deep web contains sites and pages that are often prevented from being indexed by search engines and contain unlinked content. First, let me explain that this article is intended for users who want to use the dark web for legal and needed purposes, such as finding censored news, blocked websites, and other much-needed services.
Restricted Content
- Once you have the Tor Browser installed, you can then access websites on the dark web by typing in their specific .onion address.
- It’s a space where anonymity is paramount, and it operates outside the reach of traditional search engines like Google or Bing.
- Its massive database of indexed dark web content rivals that of Torch and even goes a step further with filtering tools.
- Dark.fail is a directory that lists verified links to active and trustworthy dark websites that Google won’t let users find.
- Whether it is privacy-based tools, educational resources, or even specialty communities, the deep web has a case to the limits and restrictions of the surface.
Some may lead to malicious sites, downloading malware on your device. However, there’s no guarantee that all the links on this site are working. Depending on your preference, you can find links in well-categorized groups. OnionLinks is a library of dark web links, most importantly, active links. But it is not all bad; the dark web’s anonymity also allows well-meaning individuals, such as whistleblowers As a result, the recommended browser for accessing the dark web is the Tor (The Onion Router) browser.
Facebook Onion Site
If you get caught using its services, you can face serious trouble. Know that Awazon is an illegal marketplace that sells illegal products (like banned drugs) or stolen ID cards. The site doesn’t require an email verification, though it offers all the features and security that you want in a dark web marketplace. Awazon Marketplace is the leading dark-web marketplace that claims to provide a secure destination for anonymous trading.

Use The Tor Browser
Its longevity and reliability have made it a favorite among many Tor users. The Debian Project’s presence on the Tor network is a testament to its commitment to open-source principles. The presence of the Central Intelligence Agency (CIA) on the Tor network might come as a surprise to many. Its commitment to user privacy, combined with its comprehensive suite of tools, makes Tails an essential asset for Tor enthusiasts. Tails is a unique operating system tailored for those who prioritize privacy and security. With its focus on user privacy and a clean, user-friendly interface, Ahmia has become an indispensable tool for many Tor users.
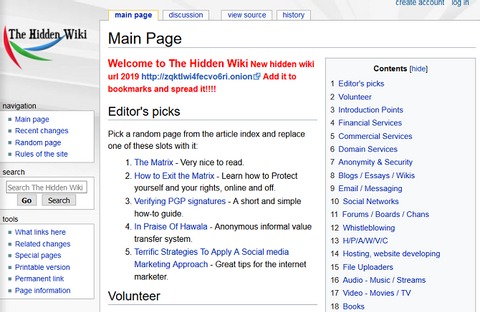
The Hidden Wiki — Collection Of Popular Dark Web Links
However, Facebook’s dark web version will still log your data, so keep that in mind. I like that you can ask the search engine to match all of your search words for exact results, or only some of them for broader search results. One of its best features is Anonymous View, which is a free proxy that masks your identity while you’re browsing sites. Plus, it lets you set your location for local results, manage safe search filtering, and there’s even an AI “Assist” tool that provides AI search results — so you don’t have to visit web pages to find your answer. And I liked that if I visited a site that had a .onion version, it prompted me to switch to that version.
Verified directories, anonymity tools, and cautious clicking make all the difference. That’s why it’s essential to rely only on trusted onion directories—sources known for link accuracy and uptime tracking. Many phishing sites imitate trusted platforms like the Hidden Wiki to trick users. To boost anonymity, many users connect to Tor through a VPN, which hides Tor usage from their internet provider.
Top 10 Dark Web Search Engines In 2026 (Tools For Staying Anonymous On The Dark Web)
So, to get into the Tor network, follow the steps I’ve listed below. The majority of the users on the dark web use the Tor (The Onion Router) browser. This provides a full month’s access to all of the features of the #1 VPN for the Dark Web. It has been estimated that a large percentage of dark web traffic is related to illegal pornography that includes underage victims. Hacker services against banks and other financial institutions are offered there.
- The site’s database covers many topics from science to fiction and is maintained by volunteers.
- If you’re feeling chatty, you can always access a chat room.
- It’s made up of websites indexed by search engines, such as Google, Yahoo, or Bing.
- That means that I2P can’t visit “.com” or “.onion” sites because the network is not connected to these servers.
- Plus, many .onion websites are created to be temporary or invite-only, so they may not even be active long enough to be indexed.
Ransomware gangs are also expected to diversify their tactics, targeting smaller companies and individual users to maximize their reach. These groups often operate on a ransomware-as-a-service (RaaS) model, renting their tools to affiliates in exchange for a share of the profits. Crypto-laundering threat actors specialize in stealing and hiding the origins of their cryptocurrency. Social media and gaming platforms are increasingly being used to recruit inexperienced hackers, further expanding these gangs’ reach. The proliferation of IoT and 5G devices will provide new attack vectors for infostealer gangs.
Download Tor Browser
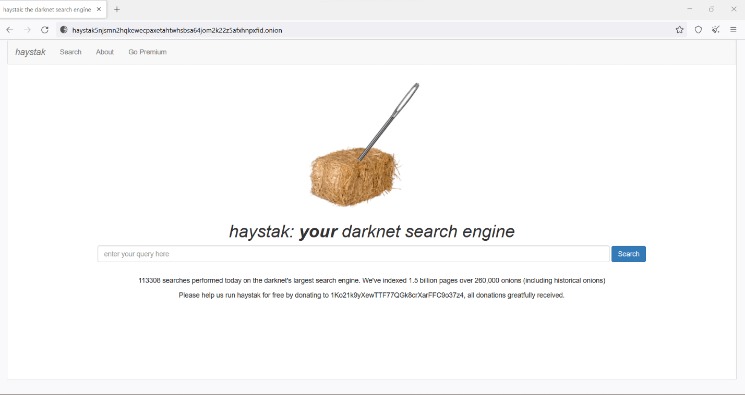
DeepSearch is an open-source search engine designed for exploring the dark web within the Tor network. It is designed to ensure user anonymity while offering access to a diverse array of information available on the dark web. Haystak is a dark web browser that offers better filtering features that help users refine their search results, enabling them to locate exactly what they need.
In other words, it’s the dark web’s version of ScienceDirect. The first website on our list is, allegedly, the largest repositories of scientific papers on the dark web. With these in mind, let’s take a closer look at the dark web sites rundown. Hackers, both white- and black-hat, can also be found scouring the depths of the dark web for things like malicious code, special hacking tools, victims, and more. A little refresher on the dark web – it’s like a gathering house, where all sorts of people congregate. In this sequel, I’m going to show you some of the not-so-clear-web’s hidden Easter eggs and how to get there.
This FAQ section was developed with the hopes of helping users understand basic aspects of Tor links, onion sites, and the deep web as a whole. Developers, journalists, educators, and advocates for privacy use onion sites as a means to share information in a way that is free and secure. Exploring the deep web responsibly requires a clear understanding of the potential it offers and being aware of its limitations—staying anonymous, not clicking suspicious links, and using verified tor sites from written onion site lists. By following these steps, you’ll surf the Tor network safely and realize the full power of verified onion links and deep web sites — with little risk and no confusion.And remember, your privacy matters — make it a priority every time you connect. The deep web is much more than just dark markets – it is a destination for journalists, researchers, developers, and advocates for privacy.On the deep web, you may find services like encrypted email, secure chat services, digital libraries, and onion resources provided by communities looking to help to protect information freedom and digital privacy.
Dark Web Threat Intelligence Analysis 2026
Additionally, I2P doesn’t rely on hidden directories that serve as a resource for .onion domains. That means that I2P can’t visit “.com” or “.onion” sites because the network is not connected to these servers. Users who wish to gain access to such information are protected by the same anonymity the publishers of the content enjoy. All of the above is why I strongly recommend using the dark web not for access to iffy or outright illegal trading of goods and services, but instead to gain access to information you might normally be blocked from. But remember, it’s essential to take all the necessary and important security steps before entering such sites on the dark web.