Recently, around 100,000 compromised ChatGPT users' login information was sold on the dark web in 2023. Attempts to monitor this activity have been made through various government and private organizations, and an examination of the tools used can be found in the Procedia Computer Science journal. Cyber crimes and hacking services for financial institutions and banks have also been offered over the dark web. Bitcoin is one of the main cryptocurrencies used in dark web marketplaces due to the flexibility and relative anonymity of the currency. Silk Road was one of the first dark web marketplaces that emerged in 2011 and has allowed for the trading of illegal drugs, weapons and identity fraud resources.
Hacking Services And Groups
For example, cyberattacks and trafficking are activities that the participants know will be incriminating. That said, anonymity comes with a dark side since criminals and malicious hackers also prefer to operate in the shadows. If an activity is deemed illegal by the governing bodies you fall under, then it would be illegal.
How Does The Dark Web Work?
This means anyone can access it, which helps to detect vulnerabilities before malicious actors take advantage. These onion addresses will remain online even if the original page disappears. Established in 2012, the platform is a time capsule that collects snapshots of websites. SecMail is one of the most popular email services on the dark web.

Communication And Email
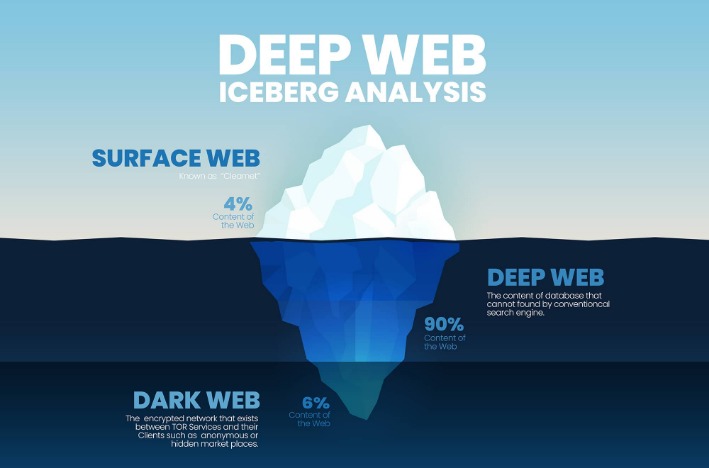
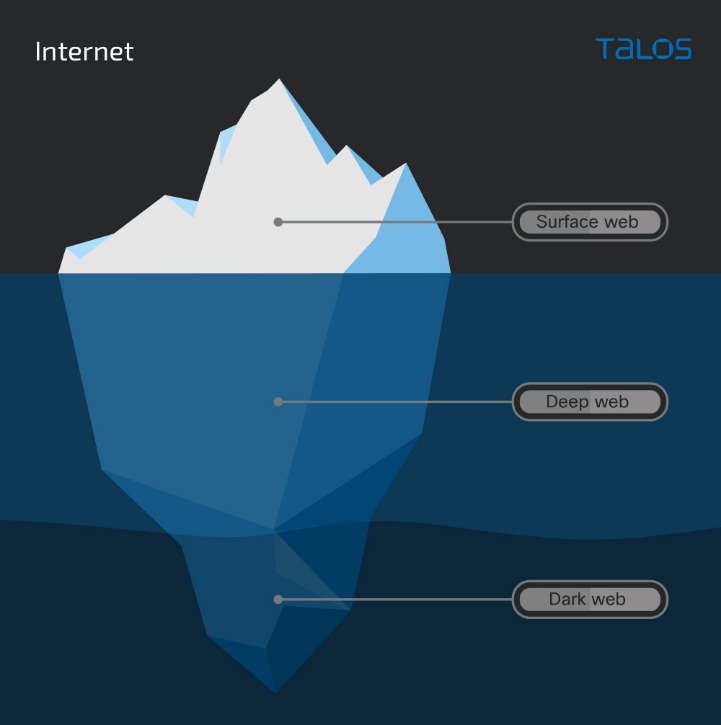
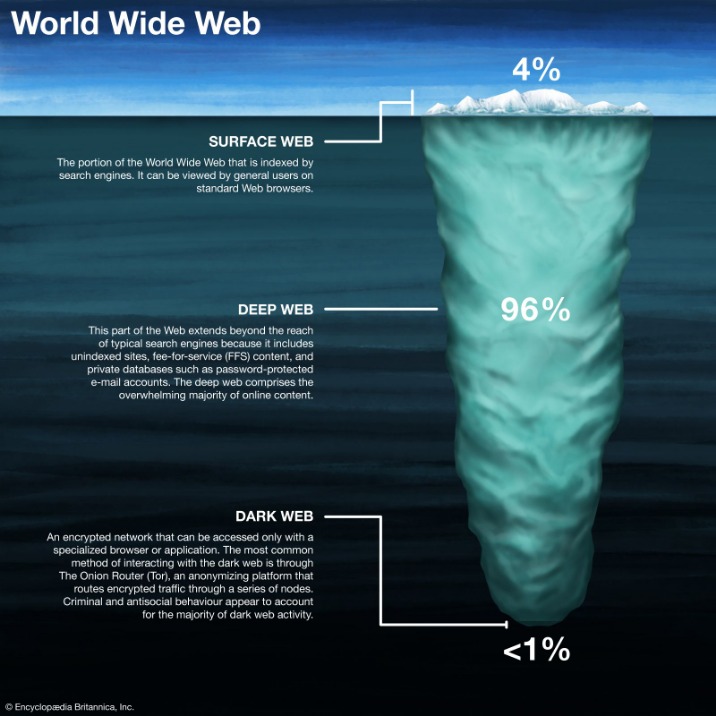
The dark web is part of the hidden web, which comprises non-indexed websites that are mostly used for illegal and illicit activity. Most people navigate the internet’s surface without a second thought—surfing websites, checking social media, shopping online, or reading news articles. For those who really want to explore the dark web, several pages called the Hidden Wiki serve as a directory of links to other .onion sites. Through Tor, users can access a number of dark web websites, including mirrored versions of surface web sites such as Facebook and The New York Times.
Like any other site of such nature, Awazon Market isn’t free from risks, so be careful while accessing it. The website has an advanced search filter and an easy-to-use interface, which makes it easy to find what someone is looking for. So, anyone wishing to access it should create an account first. For example, it has a reputation for hosting pedophile sites.
What Is Spyware? Definition, Types And Protection 2026
These pages are not indexed by search engines and are protected behind security walls, authentication forms, and passwords on the deep web. Here's a look at how the dark web works and the many ways in which people use it, both legally and illegally. While the surface web may represent most of what the average user sees, there are many more layers of hidden content to be found on the dark web. Accessing the dark web is legal in most countries, but visiting illegal sites or making illicit purchases is against the law. Companies should monitor dark web forums for leaked credentials and corporate data. As an IT leader or cybersecurity professional, understanding the dark web isn’t optional—it’s essential.

How Do Individuals Get On The Dark Web?
Part of the reason for this is lack of incentive for content creators on the dark web. Even if such sites were blocked from the regular open web, anyone using the Tor Browser could still access their email using the .onion addresses. Facebook offers an onion link to access their services, although you may find logging in difficult, as you’ll most likely appear to be signing in from a different location each time.
The Australian Federal Police (AFP) participated in a Europol-led investigation that in 2024 shut down LockBit’s primary platform along with 34 servers across the US, the UK, Europe, and Australia. Cybercriminals can build a stolen profile with telephone, address and other personal information for less than $10, according to SOCRadar’s 2024 dark web report. For CISOs, one of the biggest shifts in thinking is that the dark web is no longer just a post-breach problem. While major takedowns have disrupted parts of the dark web, it remains resilient, with new technologies and changing criminal strategies. “Try ITarian free and streamline IT operations—cloud ticketing, remote access, and patch management with zero setup cost”
- It is illegal to perform illegal acts on the dark web, regardless of the level of anonymity provided by the platform.
- Department of Justice.3 The site became a hotbed for a range of unlawful goods and services, including illegal drugs and guns for hire.
- Install Avast SecureLine VPN for iOS to protect your privacy and keep your data from falling into the wrong hands.
- Its dark web version provides the same functionality as the clear web option, while adding Tor’s anonymity layer.
- This impermanence adds to the difficulty of finding and accessing specific dark web pages.
Image Hosting — Upload & Share Images
With Proton VPN, you can route your connection through our VPN servers to the Tor network(new window). TAILS routes all connections (not just those from the browser) through the Tor network. For even greater security, you can use TAILS(new window). This is a hardened version of Firefox that, by default, automatically routes all your connections through the Tor network. The usual (and most official) way to access Tor Onion Services is by using Tor Browser for Windows, macOS, Linux, and Android(new window). Since Tor Onion Services is by far the most popular (and therefore most generally useful) dark web, we’ll focus on that here.
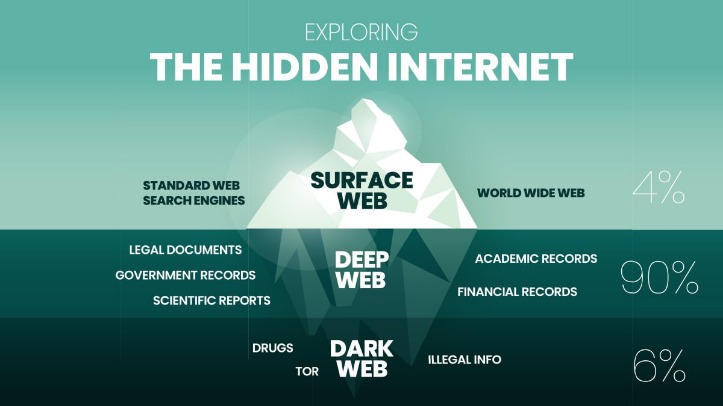
This is how users can travel through enough tangential pathways and end up on a piracy site, a politically radical forum, or viewing disturbingly violent content. Everything from blog posts in-review and pending web page redesigns, to the pages you access when you bank online, are part of the deep web. On the larger deep web, its “hidden” content is generally cleaner and safer. Without visible links, these pages are more hidden for various reasons.
Watch Out; Your ISP Could See You Using The Tor
Never share personal data such as your name, IP address, email, or financial information. Even the best privacy tools are only effective when patched against the latest threats. Ensure that your Tor browser and security software are always up to date. Here are some of the ways to reduce the risks that come with using the dark web. The accuracy of search suggestions is another concern.
The dark web provides anonymity–both for people visiting the websites and the websites themselves. While you can use Tor to anonymize your web browsing activity on normal websites, Tor also offers .onion sites, or "Tor hidden services". The moderators enforce a strict policy against posting links to illegal products or services, so you’re more likely to find safer dark web addresses here. There are some supposed ‘dark web’ search engines like Torch or Haystak is said to have indexed more .onion sites than any other search engine. For maximum security users should only access sites with the .onion suffix via the browser.